A chieve CMMC Compliance
CMMC Compliance Solutions
Addressing CMMC regulatory requirements can be a daunting task for any small organization with a limited budget, time or internal technological resources. TSI helps navigate the compliance requirements & ensure that you have the tools & resources in place to focus on growing your business while assuring you have the safeguards in place that will satisfy your industry’s compliance requirements. Please refer to the chart below for an overview of the CMMC requirements & the services TSI provides addressing those very areas.
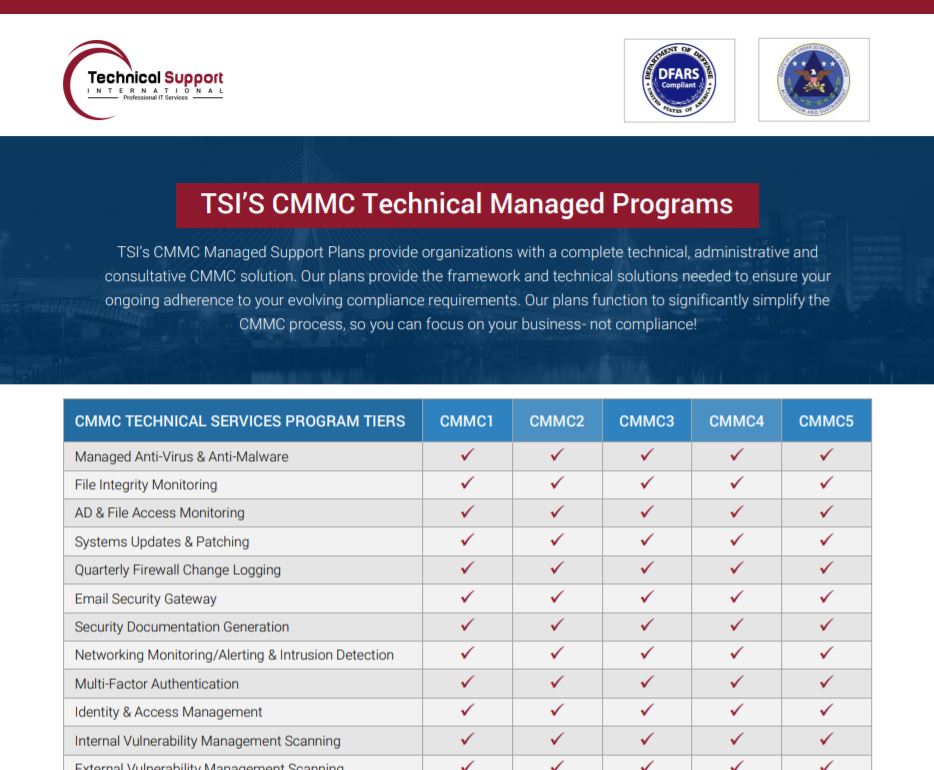
For a complete guide of the services that we provide, including the respective solution for each of the CMMC controls that we provide, please fill out the form.
C MMC Solutions and Resources
Our goal at TSI is to function as your IT compliance partner to ensure the ongoing strategic alignment between your IT compliance strategy and business objectives. To that end, we’ve developed a number of resources to help guide you through your DFARS journey and provide the required resources to effectively implement those evolving controls.
T he CMMC Compliance Guide: Prepping, Paying and Implementing IT
The Cybersecurity Maturity Model Certification (or more widely known as the CMMC) is a strategy the Department of Defense has put in place in order to start enforcing the DFARS compliance requirements. At its core, the CMMC is designed to be an assessment model and certification program intended to clarify the degree in which contractors safeguard both their own and customers’ CUI.At TSI Support International, we understand how important CMMC certification is - and we're also aware that this is one road you're not necessarily eager to travel down alone.
W hy Contractors with CUI Don’t Really Need Gov’t Software Licensing for DFARS Compliance
With the recent news that DFARS compliance requirements will start being enforced, we’ve seen a significant increase of questions concerning the role and application of ‘Government’ licensing- such as Office 365 Government or AWS GovCloud- for contractors possessing Controlled Unclassified Information (CUI). Government licensing- notably for Office 365 Government- is extremely expensive from both a subscription and an implementation standpoint.
S
ecurity Awareness Training &
Compliance Requirements
Many states in the U.S. have their own privacy laws. For example, one of the most robust privacy laws is here in the state of Massachusetts. 201 CMR 17.03 – the Massachusetts privacy law mandates training to maintain a comprehensive information security program. The training must focus on reasonably foreseeable internal and external risks to the security, confidentiality, and/or integrity of any electronic, paper, or other records containing personal information. Training must be ongoing and must be given for not only permanent employees but also temporary or contract employees.
M anufacturing and Cybersecurity: Know the Essentials
It’s no secret that the security climate on the internet is becoming more dangerous by the day. This is especially true for business professionals in the manufacturing space, where cyber attacks are only becoming more frequent and more costly with each passing year.
According to a study conducted by the Ponemon Institute, 70 percent of all organizations said that their security risk increased significantly in 2017 alone. Read the full article in National Defense Magazine.

T o Comply, or Not to Comply: The Strategic Approach to IT Compliance
Cyber security is one of the most pressing issues of our age and when you’ve got the Department of Defense watching over you, that’s a pretty big deal. A lot of these compliance requirements are very intensive and usually require implementation via a manual solution. That requires true collaboration between IT and non-IT executive staff.
What Our Clients Are Saying
“We were referred to TSI by one of our partners that used their IT services for over 15 years. We had a very rigid timeline to get the studio operational and there were a lot of loose ends and too many vendors involved. TSI - without hesitation - jumped right into the project, met our timeline and managed our vendors to get us up and running on time – and within budget. TSI’s approach to the studio build out sets the bar for IT consulting services and I look forward to continue working with them to address our IT needs."
Biotechnology Firm / Mansfield, MA





