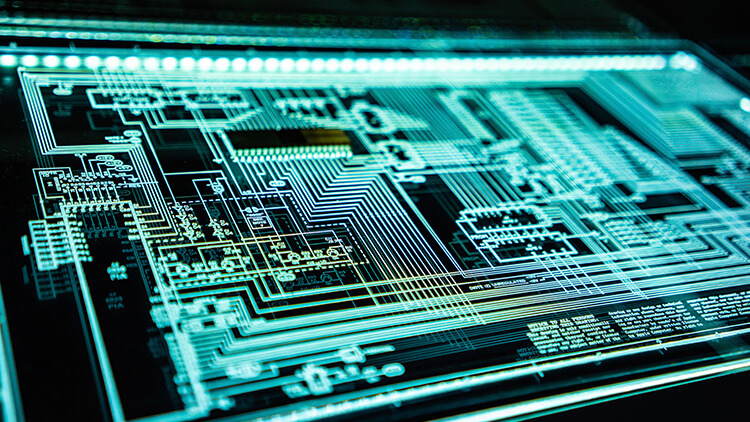
A network operations center — commonly known as a NOC — is a facility staffed by IT engineers that provide 24x7x365 management and supervision of an organization’s network environment. NOCs are typically associated with larger, enterprise-level organizations and function as the core of their organization’s technology operations. Having a NOC in place ensures that an organization’s network infrastructure is proactively managed and there are minimal interruptions to network operations.
What Do Network Operation Center’s Do?
NOCs focus primarily on:
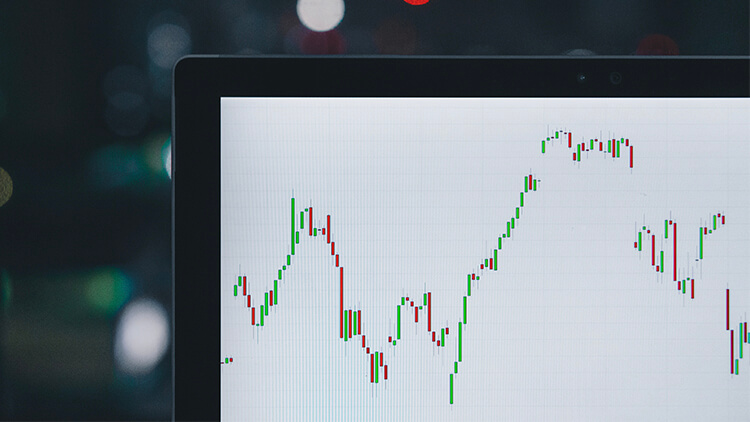
- Monitoring the network infrastructure.
- Housing and developing applications.
- Proactive remediation and monitoring.
- Addressing system alerts and events.
- Providing cybersecurity and enforcing policies.
Why Are NOCs Important to SMBs?
Despite their size, SMBs require the same — if not more — degree of responsiveness from their IT support team and the availability of their infrastructure as a larger, enterprise-sized organization. The proactive nature of a NOC provides SMBs with the support resources they require to focus on their core competencies and growing their businesses. Some of the benefits of having a NOC include but are not limited to the following:
- Reduced downtime and outages.
- 24x7x365 available support resources.
- Guaranteed SLAs.
- Improved cybersecurity posture.
- Minimized IT labor costs.
- State of the art, high-quality infrastructure.
- Customization.
Considering the pace at which technology and cybersecurity threats are evolving, it’s of the utmost importance to partner with a NOC that can be singularly focused on ensuring your organization is adequately positioned to adjust and most importantly thrive on these trends as they evolve.